Component 1: Theory Fundamentals
Comprehensive Revision Guide covering Data Representation, Information Security, Networks, and Internet Protocols. Prepared by Yerassyl Tleudin.
Data Representation
At the lowest level, all computer data is represented as binary (1s and 0s). Understanding how to convert, manipulate, and structure these bits is fundamental to computer science.
1. Number Systems & Conversion
| System | Base | Symbols | Example |
|---|---|---|---|
| Denary (Decimal) | Base-10 | 0-9 | 183 |
| Binary | Base-2 | 0, 1 | 10110111 |
| Hexadecimal | Base-16 | 0-9, A-F | B7 |
| Octal | Base-8 | 0-7 | 267 |
Advantages of Hexadecimal
- Shorter representation: One hex digit represents exactly 4 binary bits (a nibble).
- Human readability: Simpler and faster for programmers to read, write, and debug compared to long binary strings.
- Less error-prone: Fewer characters mean fewer chances of making a transcription error.
- Note: Hexadecimal does NOT take up less memory or execute faster than binary. The CPU still processes everything in binary.
Number System Conversions
2. Binary Arithmetic
You must be able to perform addition and multiplication on 8-bit binary numbers. Always watch out for an overflow error (when the result exceeds 8 bits).
! Worked Example: Binary Addition (from 2025 NIS Past Paper)
Add: 10101010 + 10111001
10101010
+ 10111001
----------
(1)01100011 <-- The 9th bit (1) is the overflow bit.Exam Tip: If asked for an 8-bit format answer, state the 8 bits (01100011) and explicitly mention that an overflow error occurred.
! Worked Example: Binary Multiplication
Multiply: 1111 * 111
1111
x 111
------
1111 (1111 * 1)
11110 (1111 * 10)
+ 111100 (1111 * 100)
-----------
11010013. Two's Complement & Subtraction
Computers use Two's Complement to represent negative integers. The Most Significant Bit (MSB) becomes a negative value (e.g., in 8-bit, the MSB is -128 instead of +128).
The 3-Step Rule for Negative Numbers
To find the Two's Complement of a negative decimal (e.g., -14):
- Write the positive binary: 14 = 0000 1110
- Flip all bits (1's Complement): 1111 0001
- Add 1: 1111 0001 + 1 = 1111 0010
! Worked Example: Binary Subtraction (2024 NIS Past Paper)
Calculate: 23 - 14 using 8-bit Two's Complement.
Step 1: Convert both to binary.
+23 = 0001 0111
-14 = 1111 0010 (Calculated using the rule above)
Step 2: Add them together (Subtraction is just adding a negative number).
0001 0111 (+23)
+ 1111 0010 (-14)
------------
1 0000 1001 (Result is +9. Discard the 9th overflow bit).4. Fractions: Fixed-Point & Floating-Point
Fixed-Point Representation
The decimal point is placed at a specific, fixed position. E.g., 4 bits for integer, 4 bits for fraction.
Pros: Simple processing.
Cons: Lacks range and precision. Cannot represent very large or very small numbers efficiently.
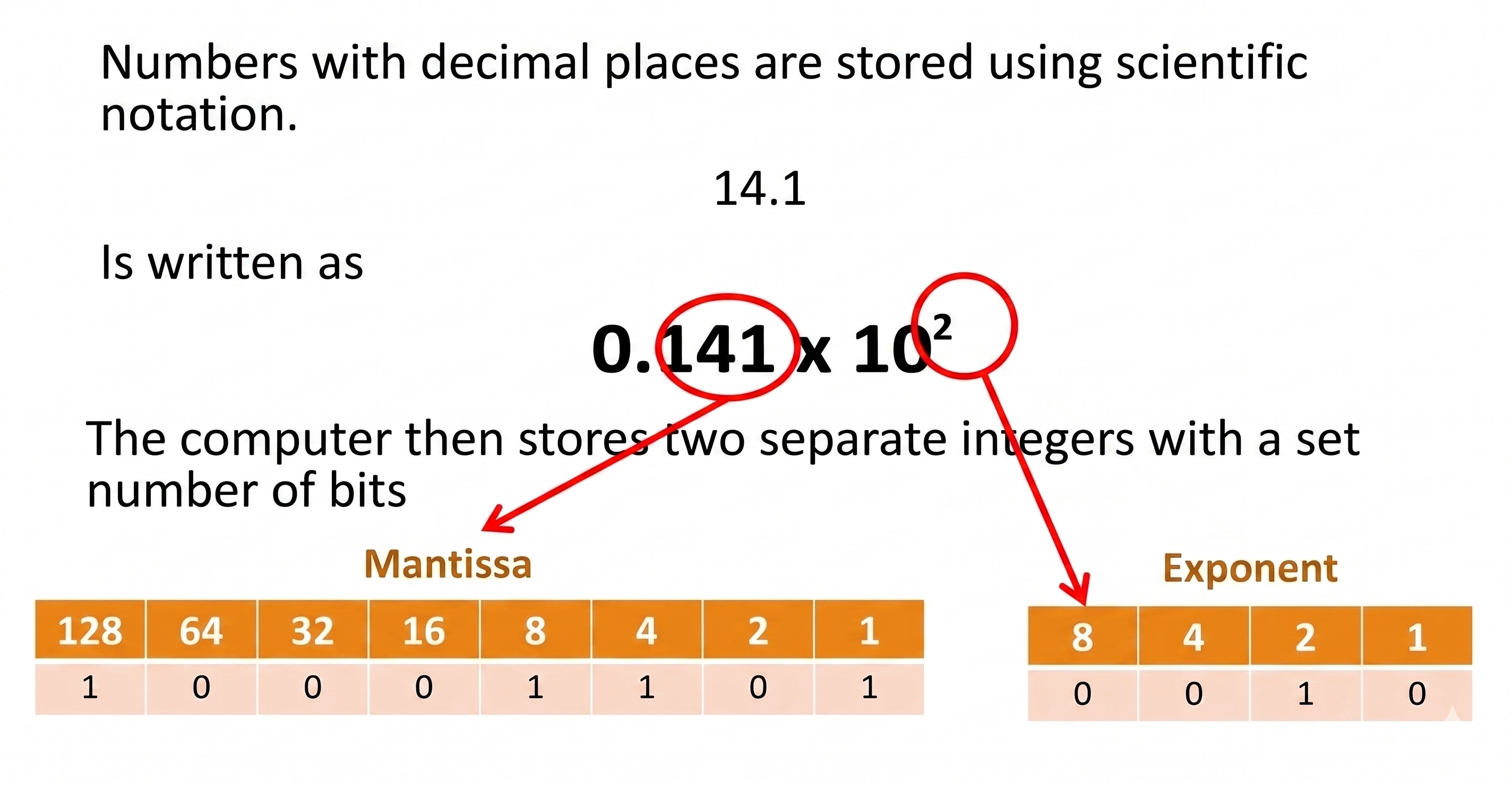
Floating-Point Representation
Numbers are stored in scientific notation format: Mantissa × BaseExponent. In binary, the base is always 2. A typical exam format uses an 8-bit or 10-bit Mantissa and a 4-bit Exponent, both using Two's Complement.
! Worked Example: Decimal to Floating-Point (2025 NIS Past Paper)
Convert 23.75 into a 12-bit mantissa and 4-bit exponent.
- Step 1: Fixed point binary. 23 = 10111. 0.75 = .11. Combined = 010111.11
- Step 2: Normalize. Move the point to get 0.1 (since it's a positive number).
Move point 5 places to the left: 0.1011111 - Step 3: Exponent. We moved it 5 places left, so Exponent = +5 = 0101
- Step 4: Pad Mantissa to 12 bits. 010111110000
Final Answer: Mantissa: 010111110000 | Exponent: 0101
The Normalization Rule
A floating-point number is normalized to maximize precision (preventing leading zeros). You must look at the first two bits of the Mantissa:
- Positive normalized numbers MUST start with: 01...
- Negative normalized numbers MUST start with: 10...
Information Security
In the modern digital world, protecting data from unauthorized access, ensuring its accuracy, and maintaining user privacy are critical. This module covers the core principles and technologies of data security.
1. Security, Privacy, and Data Integrity
| Term | Definition (Cambridge AS/A Level Standard) |
|---|---|
| Data Security | Protecting data and systems from unauthorized access, accidental loss, damage, or malicious alteration (e.g., using firewalls, passwords). |
| Data Privacy | The right of individuals to control their personal data, deciding who can access it and how it is used (e.g., GDPR compliance, consent forms). |
| Data Integrity | Maintaining the accuracy, consistency, and reliability of data over its entire life cycle. Ensuring data is not altered or corrupted during transmission or storage. |
Mixing up Security and Integrity
A system can be highly secure (no hackers can get in) but have poor data integrity (the system crashes and corrupts the files itself). Security is about protection from access; Integrity is about accuracy and correctness.
2. Data Protection Measures
Organizations use multiple layers of protection to ensure data is not lost or stolen. Two critical concepts often compared in exams are Data Backup and Disk Mirroring.
| Feature | Data Backup | Disk Mirroring (RAID 1) |
|---|---|---|
| Definition | A copy of data made at a specific point in time, stored on a separate medium or location. | Data is simultaneously written to two separate hard drives in real-time. |
| Primary Purpose | To recover data if it is accidentally deleted, corrupted, or destroyed by ransomware. | To ensure continuous system operation (high availability) if one hard drive physically fails. |
| Disadvantage | Data created between the last backup and the crash will be lost. Restoring takes time. | If a user accidentally deletes a file, it is instantly deleted from the mirrored drive too. |
Access Rights (Authorization)
Providing users with different levels of access based on their role. For example, a student (Read-Only access to grades) vs. a teacher (Read/Write access to grades). This minimizes accidental data corruption and insider threats.
3. Validation & Verification
The Airport Security Analogy
Validation is like the X-ray scanner — it checks whether your bag contains allowed items (reasonable data), but it can't tell if it's your bag. Verification is like checking your passport photo against your face — it confirms the data is correct and belongs to you.
| Type | Meaning | Examples |
|---|---|---|
| Validation | Automated computer check to ensure data is reasonable, sensible, and within acceptable boundaries before processing. |
|
| Verification | Check to ensure data is correct and matches the original source. |
|
4. Encryption
Encryption scrambles plain text into cipher text using a mathematical algorithm and a key. It does NOT prevent data interception; it prevents the intercepted data from being understood.
! Symmetric vs. Asymmetric Encryption
Symmetric Encryption: Uses the same single key to encrypt and decrypt. It is fast, but transferring the key securely to the recipient is a major risk (Key Distribution Problem).
Asymmetric Encryption: Uses a mathematically linked pair of keys (Public and Private).
1. The sender encrypts the message using the recipient's Public Key (which is shared with everyone).
2. The recipient decrypts it using their Private Key (which is kept strictly secret).
How Asymmetric Encryption Works
Insert YouTube Video Here
5. Biometrics & Ethical Issues
Biometrics uses unique physical or behavioral characteristics (fingerprint, retina scan, facial recognition) to authenticate a user.
Exam Focus: Biometrics Evaluation (from Past Papers)
Benefits: Extremely difficult to forge or steal compared to passwords. Users cannot forget them or leave them at home (like ID cards).
Security Vulnerabilities: If a biometric database is hacked, you cannot "reset" your fingerprint like you can reset a password. False positives/negatives can lock out legitimate users.
Ethical & Privacy Issues: Governments or corporations collecting biometric data raises concerns about mass surveillance, tracking without consent, and violations of personal freedom and democratic rights.
6. Blockchain Technologies
A blockchain is a decentralized, distributed, and public digital ledger. It is used to record transactions across many computers so that the record cannot be altered retroactively.

- Blocks: Data is stored in blocks. When a block is full, it is chained to the previous block.
- Hashes: Each block has a unique cryptographic hash (like a digital fingerprint). It also stores the hash of the previous block.
- Immutability: If a hacker tries to alter data in one block, its hash changes immediately. This breaks the link to the next block, invalidating the entire chain.
- Decentralization (P2P Network): There is no central server. Every participant (node) has a full copy of the blockchain. A change must reach a consensus (e.g., Proof of Work) across the network to be accepted.
Computer Networks
A computer network is a group of interconnected devices that can communicate and share resources. Understanding how these networks are structured, how data is routed, and the theoretical models behind them is essential for network engineering.
1. Network Types: LAN vs. WAN
| Feature | Local Area Network (LAN) | Wide Area Network (WAN) |
|---|---|---|
| Geographical Area | Small area (e.g., a single building, school, or home). | Large area (e.g., cities, countries, or global like the Internet). |
| Infrastructure Ownership | Owned and managed by the organization using it (e.g., school owns its routers and cables). | Leased from third-party telecommunication companies (ISPs). |
| Transmission Medium | Twisted pair copper cables (Ethernet), Wi-Fi. | Fiber-optic cables, satellite links, microwave transmission. |
| Speed & Errors | High transmission speed, low latency, fewer data errors. | Slower speeds, higher latency, higher chance of data corruption. |
Exam Tip: The "Ownership" Rule
In exams, geography alone isn't enough to define a LAN or WAN. A network covering a large university campus is still a LAN if the university owns all the cables. It only becomes a WAN if they have to pay a telecom company to cross public land.
2. Network Topologies
Topology refers to the physical or logical layout of a network. The syllabus requires knowledge of Bus, Ring, Star, and Mixed (Mesh) topologies.

| Topology | Advantages | Disadvantages |
|---|---|---|
| Bus (Single backbone cable) |
Cheap and easy to install. Requires the least amount of cable. | If the main cable breaks, the whole network fails. High risk of data collisions. |
| Ring (Closed loop) |
No data collisions (data travels in one direction). Performs well under heavy load. | If one cable or node breaks, the whole network fails. Hard to add new devices. |
| Star (Central switch) |
If one cable breaks, only that node fails. Highly secure and easy to expand. | Expensive (needs a lot of cable). If the central switch fails, the whole network goes down. |
| Mixed / Mesh (Interconnected) |
Extremely robust/reliable (self-healing routing). Multiple paths to destination. | Very expensive and complex to install and maintain physically. |
3. Network Equipment
- Switch: Connects devices in a LAN. It reads the MAC address of incoming data frames and forwards them only to the specific destination port (unlike a Hub, which broadcasts to everyone).
- Router: Connects two or more different networks (e.g., a LAN to a WAN/Internet). It reads IP addresses and determines the most efficient path for data packets.
- WAP (Wireless Access Point): Allows wireless devices to connect to a wired network using Wi-Fi (radio waves).
- Gateway: A node that connects two networks operating with different protocols (translates data formats).
- Bridge: Connects two LANs that use the same protocol, effectively combining them into a single larger LAN.
- NIC (Network Interface Card): Hardware component built into a device allowing it to connect to a network. Contains the hardcoded MAC address.
4. Packet Switching vs. Circuit Switching
! What is a Data Packet?
Before transmission, large files are broken down into small chunks called packets. A standard packet contains:
- Header: Sender's IP, Receiver's IP, Packet Sequence Number (e.g., Packet 3 of 500), and Packet Size.
- Payload: The actual raw data being sent.
- Trailer: Error checking data (Checksum) and end-of-packet marker.
| Feature | Circuit Switching | Packet Switching |
|---|---|---|
| Path Setup | A dedicated physical path is established before data is sent. | No dedicated path. Packets take the best available route independently. |
| Bandwidth | Bandwidth is reserved and wasted if no data is being sent. | Shared bandwidth. Highly efficient use of network resources. |
| Data Arrival | Data arrives strictly in order. | Packets can arrive out of order and must be reassembled at the destination. |
| Best used for... | Real-time live video, voice calls (no lag or jitter). | Emails, downloading files, browsing the web. |
| Resilience | If the dedicated line is cut, the connection drops immediately. | Highly resilient. If a router fails, packets simply reroute around the problem. |
5. The OSI Network Model
The Open Systems Interconnection (OSI) model is a conceptual 7-layer framework that standardizes the functions of a telecommunication system. It helps manufacturers ensure their hardware and software can communicate.
Mnemonic to remember the layers:
Please Do Not Throw Sausage Pizza Away.
(Physical, Data Link, Network, Transport, Session, Presentation, Application)
| Layer (Top to Bottom) | Core Functions & Responsibilities | Data Unit & Protocols |
|---|---|---|
| 7. Application | Provides network services directly to user applications (web browsers, email clients). | Data (HTTP, FTP, SMTP, POP3) |
| 6. Presentation | Formats, translates, encrypts, and compresses data so it is readable by the Application layer. | Data (SSL/TLS, JPEG, ASCII) |
| 5. Session | Establishes, maintains, and terminates connections (sessions) between two communicating devices. | Data (APIs, NetBIOS) |
| 4. Transport | Breaks data into segments. Ensures reliable end-to-end message delivery, error recovery, and flow control. | Segments (TCP, UDP) |
| 3. Network | Handles logical addressing (IP addresses) and routing packets across multiple different networks. | Packets (IP, ICMP, Routers operate here) |
| 2. Data Link | Handles physical addressing (MAC addresses) and node-to-node data transfer within the same local network. | Frames (Ethernet, MAC, Switches operate here) |
| 1. Physical | Transmits raw bit streams (1s and 0s) over physical mediums (cables, radio waves, light pulses). | Bits (Cables, Hubs, Wi-Fi waves) |
The OSI Model Explained
Insert YouTube Video Here (Visualizing data flow from Layer 7 down to Layer 1)
Internet & Protocols
The Internet is the global system of interconnected computer networks. To make this massive system work reliably, strict rules (protocols) and addressing systems (IP, MAC, DNS) must be followed.
1. Internet, Intranet, and the WWW
- The Internet: The physical global network of interconnected networks (the hardware, cables, and routers).
- World Wide Web (WWW): An information system running on top of the Internet, where documents and web resources are identified by URLs and accessible via web browsers.
- Intranet: A private network accessible only to an organization's staff (e.g., NIS internal portal). It uses the same protocols as the Internet but is blocked from public access by a firewall.
2. Addressing: MAC vs. IP Addresses
| Feature | MAC Address (Media Access Control) | IP Address (Internet Protocol) |
|---|---|---|
| Purpose | Identifies the physical device (hardware) on a Local Area Network (LAN). | Identifies the location of a device on a global network (Internet). |
| Permanence | Permanent. Hardcoded into the Network Interface Card (NIC) by the manufacturer. | Changeable (Dynamic). Assigned by the network router or ISP when you connect. |
| Format | 48 bits, written as 6 pairs of Hexadecimal digits. Example: 00-1A-2B-3C-4D-5E |
See IPv4 vs IPv6 below. |
How to find your MAC address
Open the Command Prompt (Windows) and type ipconfig /all. Look for the "Physical Address" under your active network adapter.
IPv4 vs IPv6 Formats
Because the world ran out of IPv4 addresses due to the explosion of mobile devices, IPv6 was introduced.
- IPv4: 32 bits long. Written as 4 decimal octets separated by dots. (e.g.,
192.168.1.50). Provides ~4.3 billion addresses. - IPv6: 128 bits long. Written as 8 quartets of Hexadecimal digits separated by colons. (e.g.,
2001:0db8:85a3:0000:0000:8a2e:0370:7334). Provides virtually infinite addresses.
3. URLs and the Domain Name System (DNS)
A URL (Uniform Resource Locator) is an easy-to-remember representation of an IP address. Example structure: https:// (Protocol) + www.mr-tea.net (Hostname/Domain) + /assets/image.jpg (File Location/Path).
! Exam Focus: How DNS Resolves a URL (5 Marks)
Memorize this exact sequence from the Cambridge/NIS Mark Schemes:
- The user types a URL into the browser.
- The browser checks its local cache to see if it already holds the matching IP address.
- If not, the query is sent to the local DNS Server, which contains a database of domain names and their corresponding IP addresses.
- If the local DNS does not know the IP, it passes the query to a higher-level root DNS server until it is resolved.
- The resolved IP address is sent back to the user's browser.
- The browser connects to the Web Server using that IP address and downloads the website.

4. Standard Network Protocols
A protocol is a strict set of rules governing how data is formatted, transmitted, and received across a network.
| Protocol | What it stands for | Role / Purpose |
|---|---|---|
| TCP/IP | Transmission Control Protocol / Internet Protocol | The foundational suite of protocols used to establish a connection and route data packets across the Internet. |
| HTTP / HTTPS | Hypertext Transfer Protocol (Secure) | Used for transferring multimedia web pages over the Internet between a client browser and a web server. |
| FTP | File Transfer Protocol | Used for uploading or downloading files between a client and a server on a network. |
| SMTP | Simple Mail Transfer Protocol | Used for sending email messages from a client to a mail server. |
| POP3 / IMAP | Post Office Protocol v3 | Used for retrieving/downloading email messages from a mail server. |
Why is FTP NOT suitable for live video streaming?
A classic exam question (2024 Past Paper). Answer: FTP is designed to break data into packets and re-send any lost or damaged packets to ensure perfect file integrity. Packets can arrive in a random order and must be fully reassembled before use. This causes extreme lagging and buffering, making it useless for continuous, real-time data streaming (where a dropped frame is better than a pause).
Revision Tasks
State two differences between a MAC address and an IP address.
Explain why a network operating system is appropriate for managing a centralized school database accessed by multiple teachers.
A user tries to access `www.google.com` but receives a "Server Not Found" error. However, if they type the IP address `142.250.190.46` directly, the site loads. Which network component has likely failed?
Discuss the potential ethical issues and security risks of a government collecting mandatory biometric data (fingerprints and facial scans) for all citizens. Provide at least three distinct arguments.
Exam Self-Check Quiz
Q1: Which OSI Layer is responsible for logical IP routing?
Q2: What is the primary difference between Data Security and Data Integrity?
Q3: Convert the Hexadecimal number 5C to Denary.
Q4: Name the protocol used strictly to SEND emails to a server.